This year’s International Pascal Congress 2026 will be held from June 22 to 26 in the colorful Spanish city of Salamanca. The Congress will bring together highly recognized international professionals in software development and researchers using the Object Pascal language and the Delphi tool.
Attending this event is a unique opportunity to receive cutting‑edge training on programming skills…
If you have ever built a dashboard or an operations screen, you know the problem. You want the numbers on screen to reflect what is actually happening on the server, but you also do not want to write a polling loop that fires a request every second and hammers your backend…
Software auditability is not a paperwork exercise. It is the operational proof that lets developers, security teams, and decision-makers understand what code shipped, who had access, how data moved, and whether the system behaved as intended. In the RAD Studio context, that…
Embarcadero is pleased to announce that RAD Studio 13 Florence Update 1 (RAD Studio 13.1), along with Delphi 13 Update 1 and C++Builder 13 Update 1, is available to customers starting today.
RAD Studio 13.1 Florence delivers a broad set of enhancements across the product…
AI Leapfrog: Why On-Prem Software May Win the Agentic Era
March 17, 2026
For the past decade, the software industry has treated one idea as inevitable: everything moves to SaaS.
But artificial intelligence may be about to flip that assumption on its head.While cloud platforms captured the last generation of software innovation, the next…
CodeRage 2025: Our Favorite Webinars Part 4
February 28, 2026
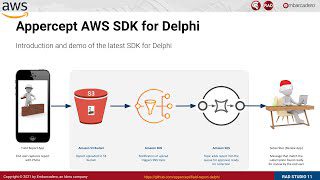
Continuing our selection of our favorite webinars from CodeRage 2025, here’s set 4. We’ve included sessions on integrating applications with Google ADK, turning ideas into mobile apps, extracting data from databases, practical applications of AI, and an AI ecosystem for…
Old Embarcadero Quality Portal Migrated to Atlassian JSM
February 27, 2026
Approximately two years ago, Embarcadero moved the public customer bug reporting and feature requests system for Delphi, C++Builder, and RAD Studio from an internally hosted instance of JIRA to Atlassian Jira Service Manager (JSM). This portal is available at…
Effective Threat Modeling for Software Applications
February 19, 2026
While the industry continues to lean heavily on automated scanning tools, the reality remains that security breaches do not result only by mere coding errors; they can also point to significant structural gaps in your application logic. For many developers, security is often…
Lifecycle Accountability: Designing Software for Long-Term Resilience
February 19, 2026
Teams don’t “lose security” because they forgot one tool. They can lose it when ownership gets fuzzy across the lifecycle, especially after the first release ships and competing priorities emerge during that flurry of activity. That framing matters, because it changes…
WebStencils and HTMX Guide v2: Now Updated for RAD Studio 13
February 18, 2026
We’re thrilled to share the updated version of our WebStencils and HTMX: Fast Modern Web Development with RAD Studio guide. Since the original release, WebStencils has grown significantly, and this new edition reflects all those improvements.
Download…