Delphi and C++Builder 11.1 enable a number of PE security flags for Windows applications by default, some of which were previously available but a little hidden.
ASLR and other recommended Windows security flags have long been supported by Delphi. In the recent 11.1 release, Embarcadero made it easier to use those flags in both Delphi and C++Builder by surfacing specific linker options, enabling them by default and also building packages and applications that are part of RAD Studio with those flags enabled.
More on these Windows PE Flags
Data Execution Prevention (DEP)
Allows the system to mark one or more pages of memory as non-executable preventing code from running from these regions of memory, and making it harder to exploit buffer overruns. You can read more about it in the Microsoft documentation here.
Address Space Layout Randomization (ASLR)
Randomly arranges the address space positions of key data areas of a process, including the base of the executable and the positions of the stack, heap, and libraries. Prevents exploitation of memory-corruption vulnerabilities. You can read more about ASLR on Wikipedia.
High-entropy 64-bit ASLR (Only in 64-bit applications)
Allows ASLR to use the entire 64-bit address space, as you can read here.
Terminal Services
Create Terminal Server aware (TSAWARE) applications. This is not related with security and covered by Microsoft here.
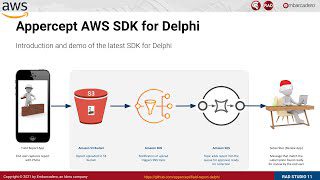
RAD Studio Improved Support
While compiler flags existed before, the RAD Studio IDE now exposes these flags as linker options. You can see below the settings for Delphi and C++ Windows compilers (thanks for the images to Jim McKeeth)


A Couple of Caveats
The ASLR compiler configuration works as expected for Delphi applications that use runtime package. For programs that link in libraries in the executable, there is a conflict with the way programs refer to delayed loaded DLL functions, which is preventing the expected behavior. This is an issue Embarcadero found after the release and would provide a fix for in the (near) future.
As you can see below, for an app with runtime packages, you get the proper configuration, as shown by SysInternals Process Explorer:

In general, these flags enforce security, and an application that uses low-level code may no longer function properly. We discovered, for example, that some old ActiveX controls no longer work in the IDE due to a conflict with the DEP flag.
If you notice any problems with your applications, you can disable these flags, but we recommend investigating the underlying problem, as some companies are requiring that all software they use to be built with all of the Microsoft recommended security flags enabled.
Up next: whether you’re a beginner or a professional, this compiler explorer tutorial will help you remember the language features essential in C++ programming.
Interested in using Embarcadero’s IDE Software? It will help you Build Apps 5x Faster With One Codebase for Windows, Android, iOS, macOS, and Linux. Request a free trial here.
Reduce development time and get to market faster with RAD Studio, Delphi, or C++Builder.
Design. Code. Compile. Deploy.
Free Delphi Community Edition Free C++Builder Community Edition






Very nice!!!
However, in order to pass Audit system, it is verifying the /GS (Buffer security check) in executables, but it is missing in Delphi Apps, what security bits represents to this or similar?
The /GS flags you quote are actually a Microsoft Visual C++ feature. There is no corresponding flag in RAD Studio with Delphi. There are other compiler options for checking for stack integrity but the /GS one seems to be specifically a MS VC++ thing as far as I can tell?
This StackOverflow article also references that question too: https://stackoverflow.com/questions/61546029/buffer-security-check-stack-cookies. The person asking the question marked Remy’s reply as a correct answer.
Hi. Can you detail on “in libraries in the executable”?
Libraries = DLLs?